Hi everyone,
we are in the midst of a measurement campaign to assess the success rate of the Direct Connection Upgrade through Relay protocol.
In this post, I want to share some early insights and spark the interest of others to participate, because in order to get data we need clients deployed in a diverse set of locations. If you want to participate please register here. It would mean a lot and gives karma points ![]()
All currently available graphs can be found on this Notion page. I will only share some interesting ones here ![]() The corresponding repository is here:
The corresponding repository is here:
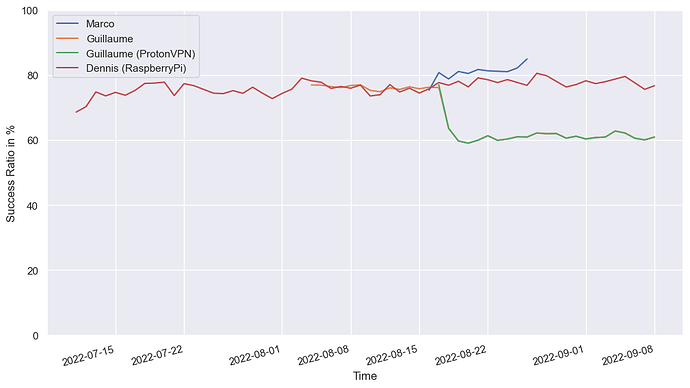
Success Rate over Time
This graph shows the hole punch success rate over time. We can see that the success rate is significantly lower for the VPN’d client. The others roughly whobble around slightly less than 80%.
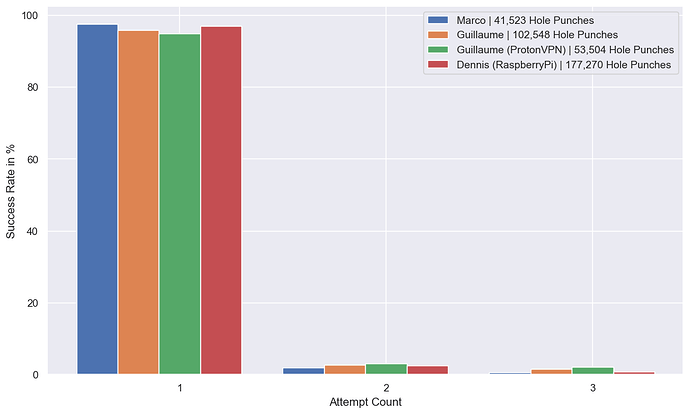
Hole Punch Attempts
The
/libp2p/dcutrprotocol is designed to hole punch the remote client three times if any attempt fails. This graph shows that if the hole punch was successful it was successful with the first attempt with a ~97% probability.
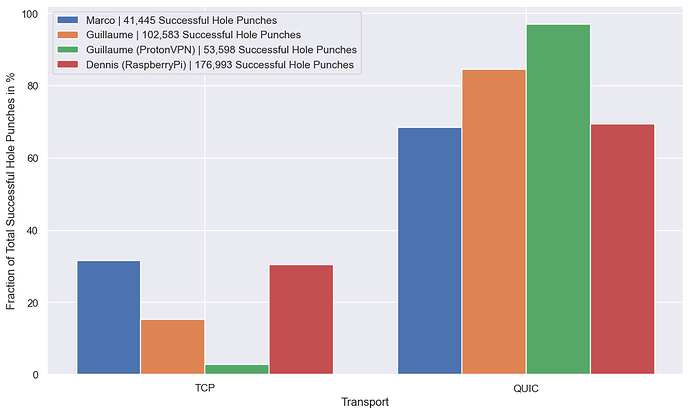
Transports of Direct Connections After a Successful Hole Punch
This graph shows that we end up with QUIC connections more often than TCP connections after a hole punch. The effect is even more pronounced for the VPN’d client. The orange client was VPN’d for half it’s uptime (see first graph - the line is right below the green one) so it makes sense that its value is between the green and blue/red bars.
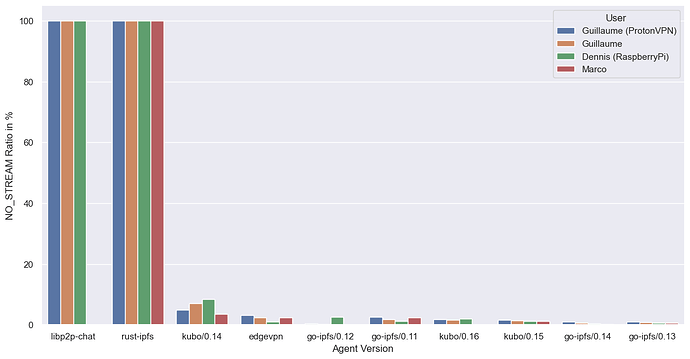
Protocol Error Ratio of All Hole Punches
It can happen that we connect to a remote peer that has advertised to support the
/libp2p/dcutrprotocol via a relay and then don’t see that stream getting opened. This graph shows the agent version distribution for those cases. This indicates a problem for therust-ipfsimplementation. Apparently, they are also using the rust libp2p hole punching implementation, so it may be worth checking out. The following hole-punch combinations were tested: Go-Go, Rust-Rust, Rust-Go but not Go-Rust. So, there may be a bug hiding there
As said above, other graphs are available in this Notion page. If you have other things you want to know about this protocol, let’s figure out how to get that ![]()
Cheers,
Dennis